Permission Manager
Permission Manager是一个为Kubernetes RBAC和用户管理提供Web UI的项目,为Kubernetes权限管理提供友好的可视化界面。
安装
从 https://github.com/sighupio/permission-manager/tree/master/deployments/kubernetes 把yaml文件下载下来,如下
[root@qd01-stop-k8s-master001 kubernetes]# ll
total 4
-rw-r--r-- 1 root root 2697 Jan 28 11:08 deploy.yml
drwxr-xr-x 2 root root 37 Jan 28 11:14 seeds
- 1.
- 2.
- 3.
- 4.
创建namespace
[root@qd01-stop-k8s-master001 kubernetes]# kubectl create namespace permission-manager
namespace/permission-manager created
- 1.
- 2.
创建秘密并进行相应更新
[rancher@qd01-stop-k8snode011 permission-manager]$ cat secret.yaml
---
apiVersion: v1
kind: Secret
metadata:
name: permission-manager
namespace: permission-manager
type: Opaque
stringData:
PORT: "4000" # port where server is exposed
CLUSTER_NAME: "kubernetes-cluster" # name of the cluster to use in the generated kubeconfig file
CONTROL_PLANE_ADDRESS: "https://10.26.29.208:6443" # full address of the control plane to use in the generated kubeconfig file
BASIC_AUTH_PASSWORD: "Admin" # password used by basic auth (username is `admin`)
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
[root@qd01-stop-k8s-master001 kubernetes]# kubectl apply -f secret.yaml
secret/permission-manager created
- 1.
- 2.
部署
[root@qd01-stop-k8s-master001 seeds]# kubectl apply -f crd.yml
Warning: apiextensions.k8s.io/v1beta1 CustomResourceDefinition is deprecated in v1.16+, unavailable in v1.22+; use apiextensions.k8s.io/v1 CustomResourceDefinition
customresourcedefinition.apiextensions.k8s.io/permissionmanagerusers.permissionmanager.user created
[root@qd01-stop-k8s-master001 seeds]# kubectl apply -f seed.yml
clusterrole.rbac.authorization.k8s.io/template-namespaced-resources___operation created
clusterrole.rbac.authorization.k8s.io/template-namespaced-resources___developer created
clusterrole.rbac.authorization.k8s.io/template-cluster-resources___read-only created
clusterrole.rbac.authorization.k8s.io/template-cluster-resources___admin created
[root@qd01-stop-k8s-master001 kubernetes]# kubectl apply -f deploy.yml
service/permission-manager created
deployment.apps/permission-manager created
serviceaccount/permission-manager created
clusterrole.rbac.authorization.k8s.io/permission-manager created
Warning: rbac.authorization.k8s.io/v1beta1 ClusterRoleBinding is deprecated in v1.17+, unavailable in v1.22+; use rbac.authorization.k8s.io/v1 ClusterRoleBinding
clusterrolebinding.rbac.authorization.k8s.io/permission-manager created
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
以上就把permission-manager部署好了,Warning信息可忽略或者自行修改yaml文件中api版本为rbac.authorization.k8s.io/v1
使用ingress暴露服务
创建ingress.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: permission-manager-ingress
namespace: permission-manager
annotations:
kubernetes.io/ingress.class: nginx
spec:
rules:
- host: permission.kubeops.net
http:
paths:
- pathType: Prefix
path: /
backend:
service:
name: permission-manager
port:
number: 4000
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
[root@qd01-stop-k8s-master001 kubernetes]# kubectl apply -f ingress.yaml
[root@qd01-stop-k8s-master001 kubernetes]# kubectl get ing -n permission-manager
Warning: extensions/v1beta1 Ingress is deprecated in v1.14+, unavailable in v1.22+; use networking.k8s.io/v1 Ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
permission-manager-ingress <none> permission.kubeops.net 10.26.29.202,10.26.29.203 80 4m8s
- 1.
- 2.
- 3.
- 4.
- 5.
自行添加dns解析,然后浏览器访问permission.kubeops.net,使用用户名密码(在secret中设置的)登录
登录
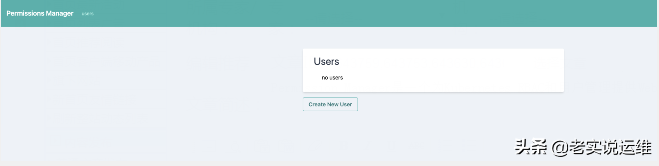
目前没有任何的用户,我们可以创建一个普通用户测试下
创建用户
点击Create New User
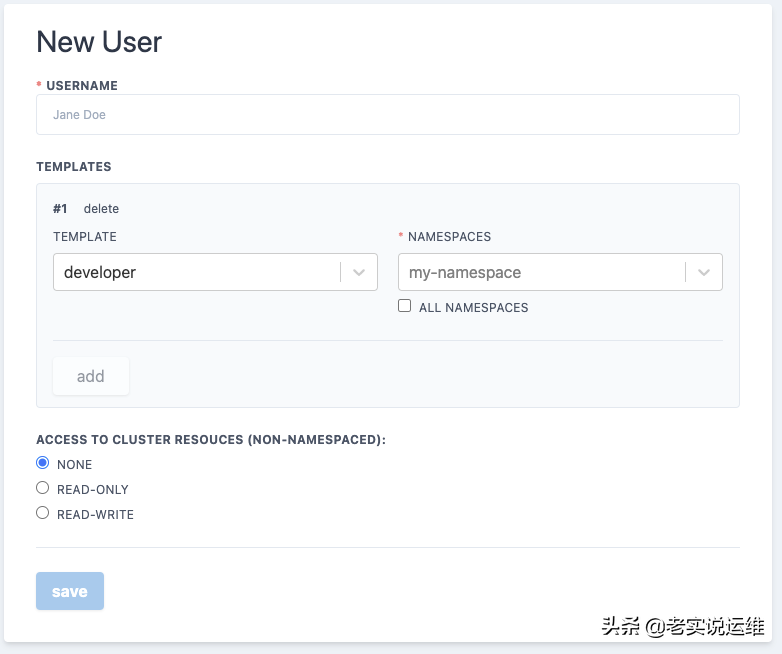
填写相关信息
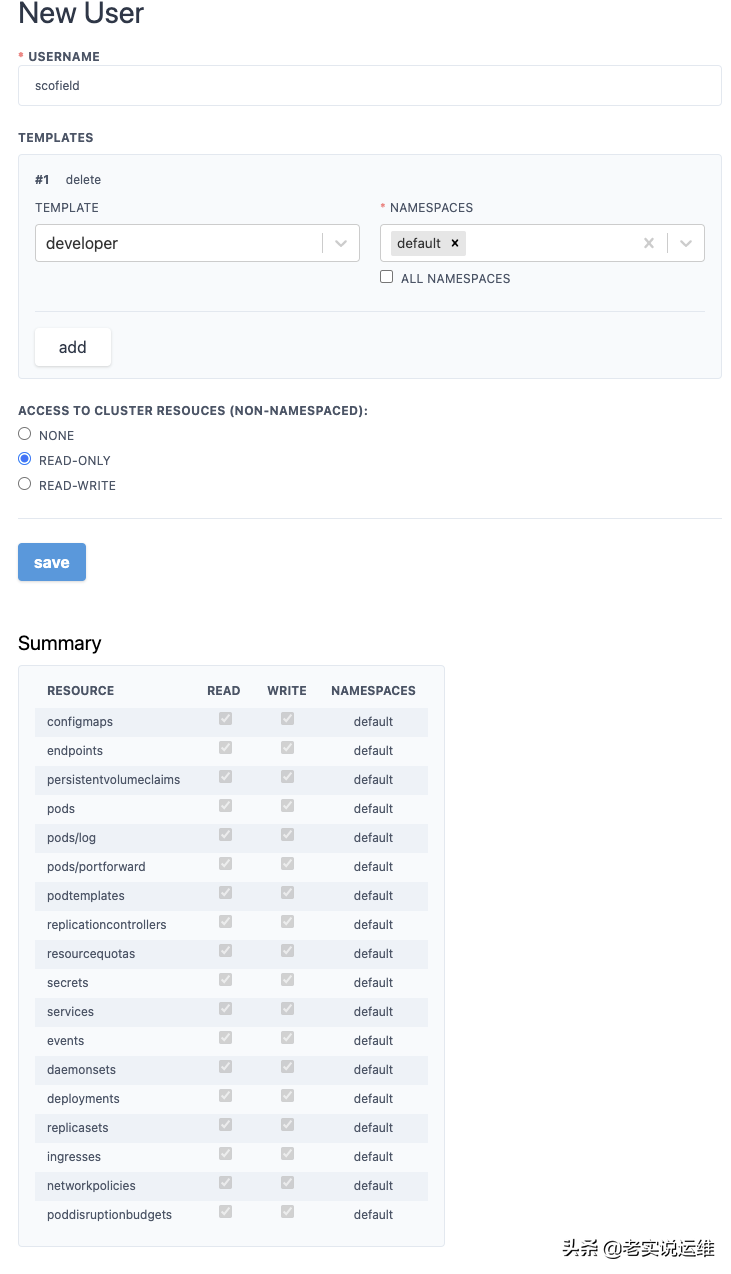
然后点击Save即可
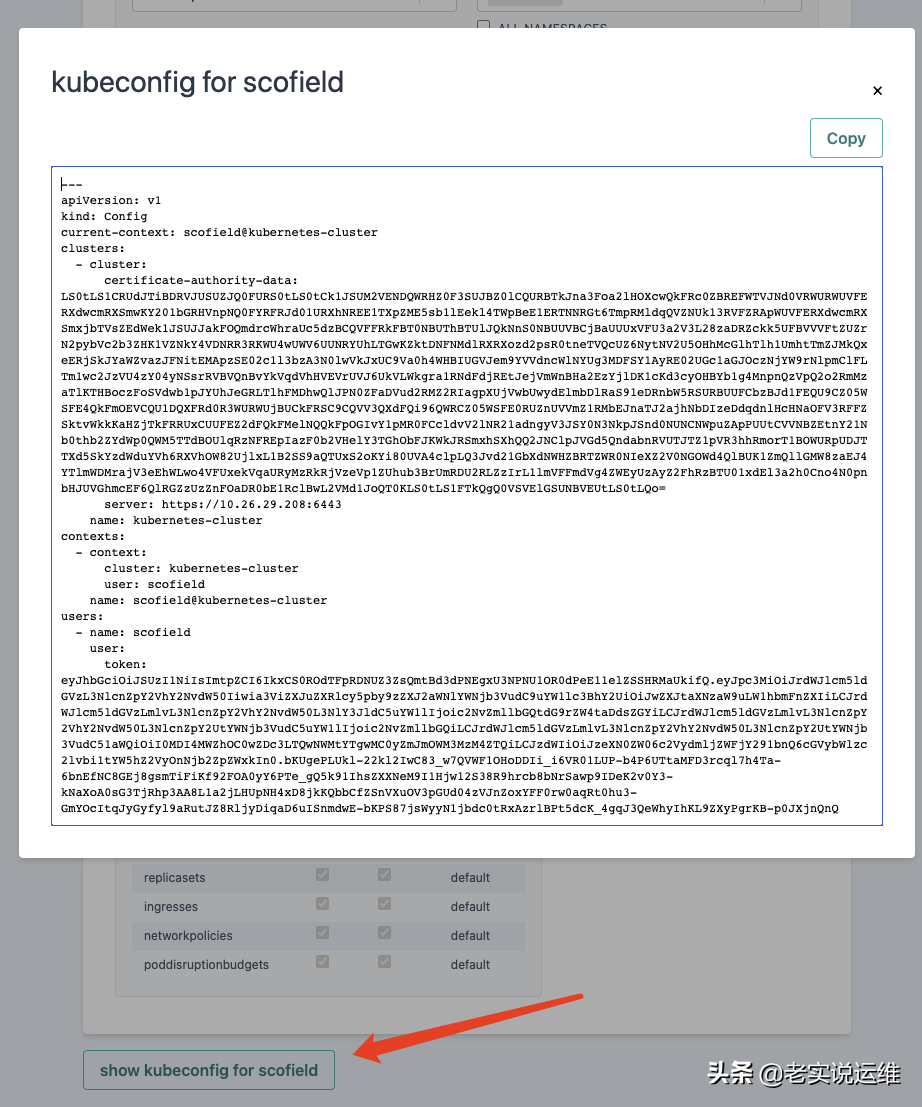
在用户信息下可以查看生成的config文件
测试
保存config文件,然后使用这个配置文件访问集群
我这里把config文件拷贝到本地,重命名为scofield,使用kubectl测试
[root@qd01-stop-k8s-master001 kubernetes]# kubectl --kubeconfig=scofield get po
No resources found in default namespace.
[root@qd01-stop-k8s-master001 kubernetes]# kubectl --kubeconfig=scofield get po -n argo
Error from server (Forbidden): pods is forbidden: User "system:serviceaccount:permission-manager:scofield" cannot list resource "pods" in API group "" in the namespace "argo"
- 1.
- 2.
- 3.
- 4.
- 5.
从以上输出可以看出,我分别查询的两个namespace,分别是default和argo,但是只有default这个命名空间有权限,而argo这个命名空间是没有权限操作的。这跟我们在创建用户是赋予的权限是一致的。
更多信息请查看官网




























