1. 事件描述
2020年12月,FireEye发现一起针对许多组织(主要是针对美国科技公司)的大规模网络攻击已经持续了几个月。这次网络攻击具有一定程度的复杂性,导致外国政府迅速介入,这次攻击中的战术和技术细节非常出色。攻击者没有进行常规的网络钓鱼或者漏洞利用攻击,而是进行了精心设计的供应链攻击。在本文中,我们重点分析了Solarwinds供应链中使用的后门(SUNBURST)及其攻击载荷之一(TEARDROP)的一些功能,包括对SUNBURST的哈希编码字符串进行彻底的模糊处理以及对TEARDROP的控制流和解密方法的分析。
2. 技术细节分析
SUNBURST后门的技术细节已经被很多公司和组织分析透彻,这使我们可以专注于我们感兴趣的一个功能上进行深度分析,我们将分析后门精心设计的免杀方法。
SUNBURST所采用的规避技术在概念上类似于沙箱规避。沙盒规避的目的是确保恶意软件不会在检测恶意软件的虚拟机上运行。
后门文件的黑名单不是以可读字符串数组的形式给出的。而是将可读字符串替换为FNV-1a哈希值。通常的恶意软件都会采用此功能,,除了最近的一些恶意软件会使用FNV-1a,而不是SHA256和CRC32校验和,但这个后门厉害的地方在于它保持了代码合法性。
后门作者对仅将进程和服务列入黑名单并不满意,他们还将某些设备驱动程序和IP地址的整个范围列入了黑名单,通过将受感染机器的IP转换为域名,该功能用于将所有内部Solarwinds域都列入了黑名单。这告诉我们,不仅攻击者决定使用Solarwinds攻击Uber到达目标,而且还详细了解了Solarwinds内部网络的拓扑结构。总体而言,嵌入在SUNBURST中的哈希编码字符串列表是SUNBURST加入黑名单的200多个域。结果表明,即使是最先进,最顽强的攻击者也不认为自己是无敌的,他们相信自己足够立于不败之地。
可在Addeneum I中找到SUNBURST中包含的FNV-1a混淆字符串的完整列表。
毫无疑问,这种攻击是一项令人难以置信的大规模黑客技术成就。250多个组织被SolarWinds后门感染,其中一半在美国,在推送恶意代码时,他们确保遵循Solarwinds的编码约定;他们在其初始有效载荷中包含了“逻辑漏洞”,以将恶意活动从初始感染推迟整整两周,并进行动态分析。他们将横向移动限制为使用被盗但有效的用户凭据进行的合法操作。出于所有这些原因,值得注意的是,这种Übermensch层的攻击被用来部署TEARDROP,这仅仅是人为的恶意软件删除程序。
在发现之时,TEARDROP是一种新的攻击载荷,从未见过,甚至可能是针对这种攻击量身定制的。它仅针对少数几个目标部署,TEARDROP在内存中运行,但是它确实注册了Windows服务,还会编辑注册表。
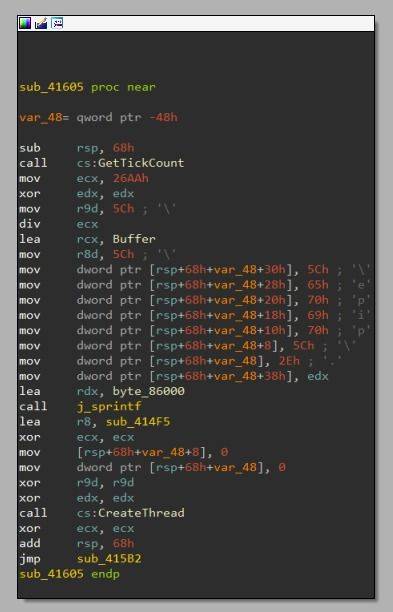
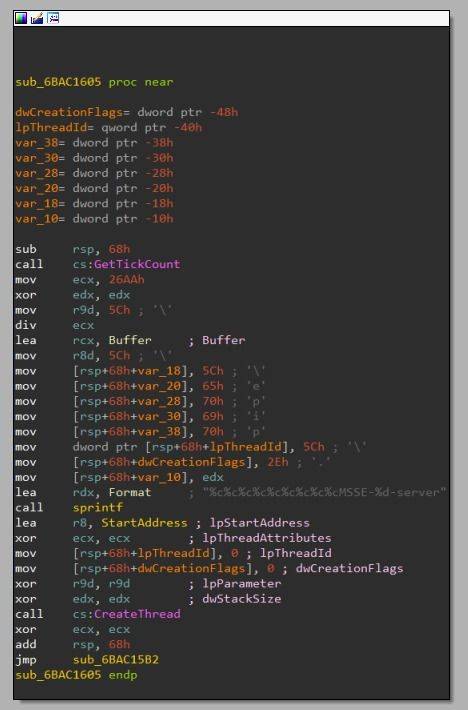
TEARDROP的控制流程非常简单,在服务执行期间调用DLL导出函数Tk_CreateImageType,该函数将JPEG图像写入当前目录,其名称各不相同;赛门铁克披露过upbeat_anxiety.jpg和festive_computer.jpg,FireEye披露过gracious_truth.jpg。在未经训练的人看来,这些似乎是人为命名的。但是更有可能是通过将两个硬编码单词连接在一起而在任意计算机上随机生成的,而该机器是用来编译该恶意软件的。
然后TEARDROP使用自制密码和硬编码密0x96钥执行解密。使用以下方法来实现该过程:
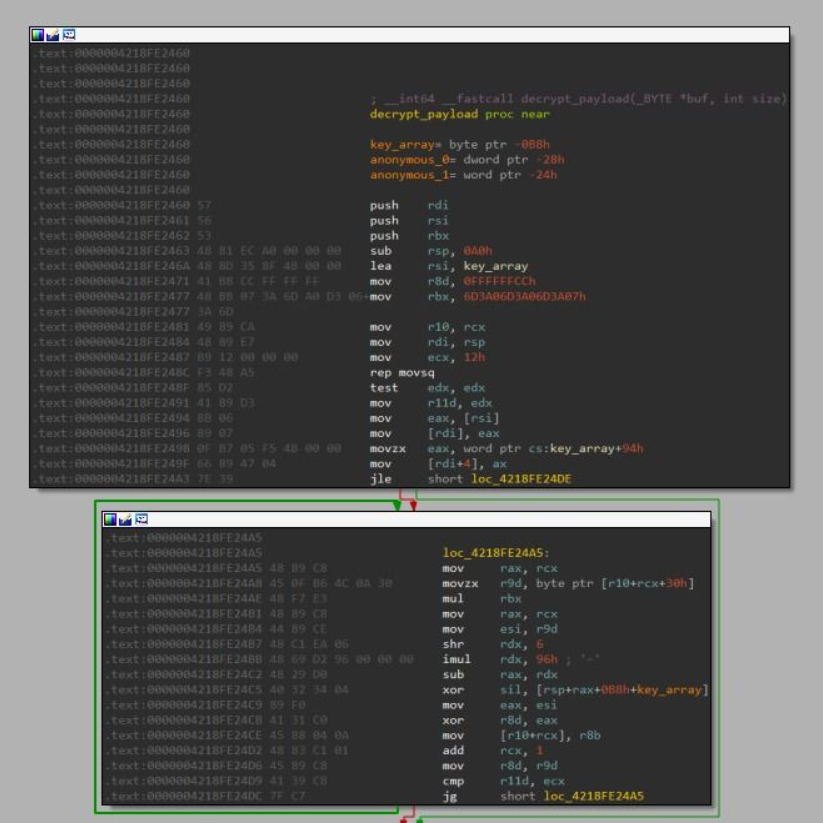
从较高的角度看,这就像某种自制PRNG,它决定每次使用哪个密钥字节。当动态运行时,生成的键索引可以简单地映射到0, 1, 2, ..., 149, 0, 1, ...等等。事实证明,这不是PRNG,而是对模运算的编译器优化实现。
一旦了解了优化,解密代码就等同于以下内容:
- CTXT_START_OFFSET = 0x30
- KEY_LENGTH = 0x96
- PREV_CTXT_BYTE_INITIAL_DEFAULT = 0xcc
- prev_ctxt_byte = PREV_CTXT_BYTE_INITIAL_DEFAULT
- for i, ctxt_byte in enumerate(ciphertext[CTXT_START_OFFSET:]):
- ptxt_byte = ctxt_byte ^ (prev_ctxt_byte ^ key[i % KEY_LENGTH])
- plaintext[i] = ptxt_byte
- prev_ctxt_byte = ctxt_byte
因此,原始加密是一个简单的XOR,然后还将每个密文字节与前一个密文字节进行XOR,没有人会随机针对内存中二进制Blob的Kasiski攻击,以期遇到XOR密文。
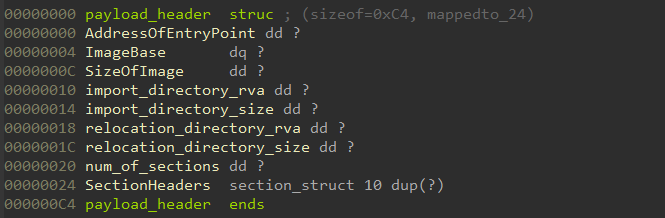
解密后的有效负载具有以下自定义header格式,其读取方式类似于正确的PE header:
第一幅图显示了在TEARDROP上找到的解密BEACON有效载荷的代码,第二幅图显示了一个已知BEACON样本的代码,PE的基本地址一样。
TEARDROP的BEACON有效载荷
TEARDROP的构建方式摈弃了BEACON,它是Cobalt Strike 附带的有效载荷。根据Cobalt Strike网站的说法,BEACON的目的是为高级攻击者建模。它支持跨各种协议的网络横向移动,用于C2签入的“被动”和“主动”模式,以及可用于模仿其他恶意软件或与目标网络的合法流量融合的可配置C2通信方案。
3. 分析总结
如果我们在这次攻击事件发生后不得不做个总结,那就是“纵深防御”。似乎我们一直以来都是这样的陈词滥调,但它源于美国国家安全局(NSA)在2012年发表的一篇论文,其背后的原理是合理且相关的:不要将所有精力都花在建一堵墙上。没有完美的围墙,总有一天,有人会穿过这面墙。
通过分析SUNBURST和TEARDROP的二进制文件,我们了解到,即使这个非常成功的攻击也存在问题。为了确保这一点,必须创建大量的域和进程黑名单。
0x04 附录I:SUNBURST中包含的FNV-1a混淆字符串列表
- Processes:
- 2597124982561782591 = apimonitor-x64
- 2600364143812063535 = apimonitor-x86
- 13464308873961738403 = autopsy64
- 4821863173800309721 = autopsy
- 12969190449276002545 = autoruns64
- 3320026265773918739 = autoruns
- 12094027092655598256 = autorunsc64
- 10657751674541025650 = autorunsc
- 11913842725949116895 = binaryninja
- 5449730069165757263 = blacklight
- 292198192373389586 = cff explorer
- 12790084614253405985 = cutter
- 5219431737322569038 = de4dot
- 15535773470978271326 = debugview
- 7810436520414958497 = diskmon
- 13316211011159594063 = dnsd
- 13825071784440082496 = dnspy
- 14480775929210717493 = dotpeek32
- 14482658293117931546 = dotpeek64
- 8473756179280619170 = dumpcap
- 3778500091710709090 = evidence center
- 8799118153397725683 = exeinfope
- 12027963942392743532 = fakedns
- 576626207276463000 = fakenet
- 7412338704062093516 = ffdec
- 682250828679635420 = fiddler
- 13014156621614176974 = fileinsight
- 18150909006539876521 = floss
- 10336842116636872171 = gdb
- 12785322942775634499 = hiew32demo
- 13260224381505715848 = hiew32
- 17956969551821596225 = hollows_hunter
- 8709004393777297355 = idaq64
- 14256853800858727521 = idaq
- 8129411991672431889 = idr
- 15997665423159927228 = ildasm
- 10829648878147112121 = ilspy
- 9149947745824492274 = jd-gui
- 3656637464651387014 = lordpe
- 3575761800716667678 = officemalscanner
- 4501656691368064027 = ollydbg
- 10296494671777307979 = pdfstreamdumper
- 14630721578341374856 = pe-bear
- 4088976323439621041 = pebrowse64
- 9531326785919727076 = peid
- 6461429591783621719 = pe-sieve32
- 6508141243778577344 = pe-sieve64
- 10235971842993272939 = pestudio
- 2478231962306073784 = peview
- 9903758755917170407 = peview
- 14710585101020280896 = ppee
- 13611814135072561278 = procdump64
- 2810460305047003196 = procdump
- 2032008861530788751 = processhacker
- 27407921587843457 = procexp64
- 6491986958834001955 = procexp
- 2128122064571842954 = procmon
- 10484659978517092504 = prodiscoverbasic
- 8478833628889826985 = py2exedecompiler
- 10463926208560207521 = r2agent
- 7080175711202577138 = rabin2
- 8697424601205169055 = radare2
- 7775177810774851294 = ramcapture64
- 16130138450758310172 = ramcapture
- 506634811745884560 = reflector
- 18294908219222222902 = regmon
- 3588624367609827560 = resourcehacker
- 9555688264681862794 = retdec-ar-extractor
- 5415426428750045503 = retdec-bin2llvmir
- 3642525650883269872 = retdec-bin2pat
- 13135068273077306806 = retdec-config
- 3769837838875367802 = retdec-fileinfo
- 191060519014405309 = retdec-getsig
- 1682585410644922036 = retdec-idr2pat
- 7878537243757499832 = retdec-llvmir2hll
- 13799353263187722717 = retdec-macho-extractor
- 1367627386496056834 = retdec-pat2yara
- 12574535824074203265 = retdec-stacofin
- 16990567851129491937 = retdec-unpacker
- 8994091295115840290 = retdec-yarac
- 13876356431472225791 = rundotnetdll
- 14968320160131875803 = sbiesvc
- 14868920869169964081 = scdbg
- 106672141413120087 = scylla_x64
- 79089792725215063 = scylla_x86
- 5614586596107908838 = shellcode_launcher
- 3869935012404164040 = solarwindsdiagnostics
- 3538022140597504361 = sysmon64
- 14111374107076822891 = sysmon64
- 7982848972385914508 = task explorer
- 8760312338504300643 = task explorer-x64
- 17351543633914244545 = tcpdump
- 7516148236133302073 = tcpvcon
- 15114163911481793350 = tcpview
- 15457732070353984570 = vboxservice
- 16292685861617888592 = win32_remote
- 10374841591685794123 = win64_remotex64
- 3045986759481489935 = windbg
- 17109238199226571972 = windump
- 6827032273910657891 = winhex64
- 5945487981219695001 = winhex
- 8052533790968282297 = winobj
- 17574002783607647274 = wireshark
- 3341747963119755850 = x32dbg
- 14193859431895170587 = x64dbg
- 17439059603042731363 = xwforensics64
- 17683972236092287897 = xwforensics
- 700598796416086955 = redcloak
- 3660705254426876796 = avgsvc
- 12709986806548166638 = avgui
- 3890794756780010537 = avgsvca
- 2797129108883749491 = avgidsagent
- 3890769468012566366 = avgsvcx
- 14095938998438966337 = avgwdsvcx
- 11109294216876344399 = avgadminclientservice
- 1368907909245890092 = afwserv
- 11818825521849580123 = avastui
- 8146185202538899243 = avastsvc
- 2934149816356927366 = aswidsagent
- 13029357933491444455 = aswidsagenta
- 6195833633417633900 = aswengsrv
- 2760663353550280147 = avastavwrapper
- 16423314183614230717 = bccavsvc
- 2532538262737333146 = psanhost
- 4454255944391929578 = psuaservice
- 6088115528707848728 = psuamain
- 13611051401579634621 = avp
- 18147627057830191163 = avpui
- 17633734304611248415 = ksde
- 13581776705111912829 = ksdeui
- 7175363135479931834 = tanium
- 3178468437029279937 = taniumclient
- 13599785766252827703 = taniumdetectengine
- 6180361713414290679 = taniumendpointindex
- 8612208440357175863 = taniumtracecli
- 8408095252303317471 = taniumtracewebsocketclient64
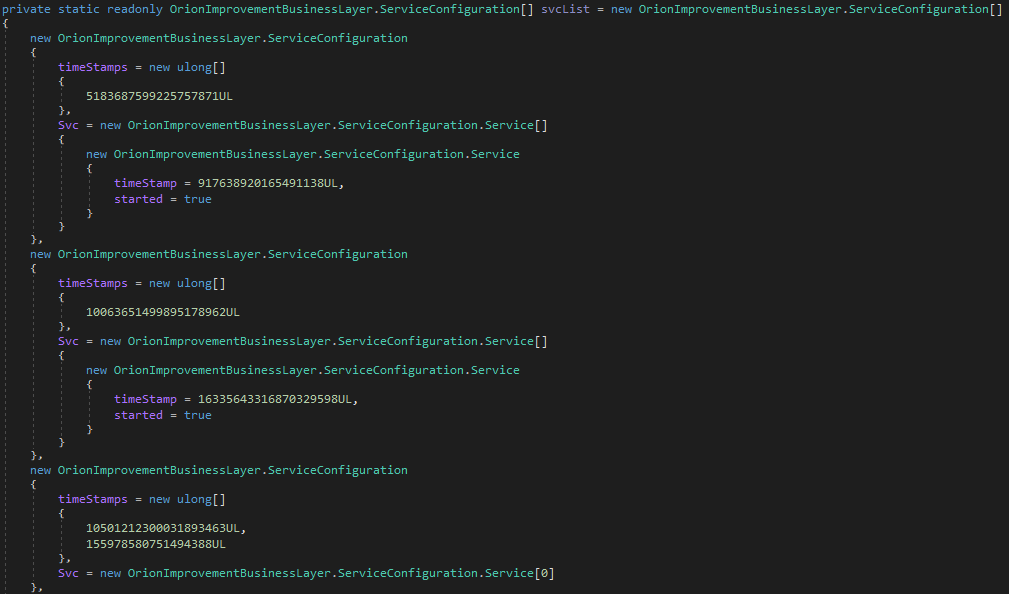
- Services:
- windows Defender:
- 5183687599225757871 = msmpeng
- 917638920165491138 = windefend
- Windows Sense:
- 10063651499895178962 = mssense
- 16335643316870329598 = sense
- Windows Sensor:
- 10501212300031893463 = microsoft.tri.sensor
- 155978580751494388 = microsoft.tri.sensor.updater
- NIST:
- 17204844226884380288 = cavp
- Carbon Black:
- 5984963105389676759 = cb
- 11385275378891906608 = carbonblack
- 13693525876560827283 = carbonblackk
- 17849680105131524334 = cbcomms
- 18246404330670877335 = cbstream
- CrowdStrike:
- 8698326794961817906 = csfalconservice
- 9061219083560670602 = csfalconcontainer
- 11771945869106552231 = csagent
- 9234894663364701749 = csdevicecontrol
- 8698326794961817906 = csfalconservice
- FireEye:
- 15695338751700748390 = xagt
- 640589622539783622 = xagtnotif
- 9384605490088500348 = fe_avk
- 6274014997237900919 = fekern
- 15092207615430402812 = feelam
- 3320767229281015341 = fewscservice
- ESET:
- 3200333496547938354 = ekrn
- 14513577387099045298 = eguiproxy
- 607197993339007484 = egui
- 15587050164583443069 = eamonm
- 9559632696372799208 = eelam
- 4931721628717906635 = ehdrv
- 2589926981877829912 = ekrnepfw
- 17997967489723066537 = epfwwfp
- 14079676299181301772 = ekbdflt
- 17939405613729073960 = epfw
- F-SECURE:
- 521157249538507889 = fsgk32st
- 14971809093655817917 = fswebuid
- 10545868833523019926 = fsgk32
- 15039834196857999838 = fsma32
- 14055243717250701608 = fssm32
- 5587557070429522647 = fnrb32
- 12445177985737237804 = fsaua
- 17978774977754553159 = fsorsp
- 17017923349298346219 = fsav32
- 17624147599670377042 = f-secure gatekeeper handler starter
- 16066651430762394116 = f-secure network request broker
- 13655261125244647696 = f-secure webui daemon
- 3421213182954201407 = fsma
- 14243671177281069512 = fsorspclient
- 16112751343173365533 = f-secure gatekeeper
- 3425260965299690882 = f-secure hips
- 9333057603143916814 = fsbts
- 3413886037471417852 = fsni
- 7315838824213522000 = fsvista
- 13783346438774742614 = f-secure filter
- 2380224015317016190 = f-secure recognizer
- 3413052607651207697 = fses
- 3407972863931386250 = fsfw
- 10393903804869831898 = fsdfw
- 3421197789791424393 = fsms
- 541172992193764396 = fsdevcon
- Drivers:
- 17097380490166623672 = cybkerneltracker.sys
- 15194901817027173566 = atrsdfw.sys
- 12718416789200275332 = eaw.sys
- 18392881921099771407 = rvsavd.sys
- 3626142665768487764 = dgdmk.sys
- 12343334044036541897 = sentinelmonitor.sys
- 397780960855462669 = hexisfsmonitor.sys
- 6943102301517884811 = groundling32.sys
- 13544031715334011032 = groundling64.sys
- 11801746708619571308 = safe-agent.sys
- 18159703063075866524 = crexecprev.sys
- 835151375515278827 = psepfilter.sys
- 16570804352575357627 = cve.sys
- 1614465773938842903 = brfilter.sys
- 12679195163651834776 = brcow_x_x_x_x.sys
- 2717025511528702475 = lragentmf.sys
- 17984632978012874803 = libwamf.sys
- domain names:
- 1109067043404435916 = swdev.local
- 15267980678929160412 = swdev.dmz
- 8381292265993977266 = lab.local
- 3796405623695665524 = lab.na
- 8727477769544302060 = emea.sales
- 10734127004244879770 = cork.lab
- 11073283311104541690 = dev.local
- 4030236413975199654 = dmz.local
- 7701683279824397773 = pci.local
- 5132256620104998637 = saas.swi
- 5942282052525294911 = lab.rio
- 4578480846255629462 = lab.brno
- 16858955978146406642 = apac.lab
- HTTP:
- 8873858923435176895 = expect
- 6116246686670134098 = content-type
- 2734787258623754862 = accept
- 6116246686670134098 = content-type
- 7574774749059321801 = user-agent
- 1475579823244607677 = 100-continue
- 11266044540366291518 = connection
- 9007106680104765185 = referer
- 13852439084267373191 = keep-alive
- 14226582801651130532 = close
- 15514036435533858158 = if-modified-since
- 16066522799090129502 = date
本文翻译自:https://research.checkpoint.com/2020/sunburst-teardrop-and-the-netsec-new-normal/