- [WindowsIntelPT](https://github.com/intelpt/WindowsIntelPT)
- [WinIPT](https://github.com/ionescu007/winipt)
- [Intel® Debug Extensions for WinDbg* for Intel® Processor Trace](https://software.intel.com/en-us/intel-system-studio-2019-windbg-pt-user-guide-windows-introducing-the-intel-debug-extensions-for-windbg-for-intel-processor-trace)
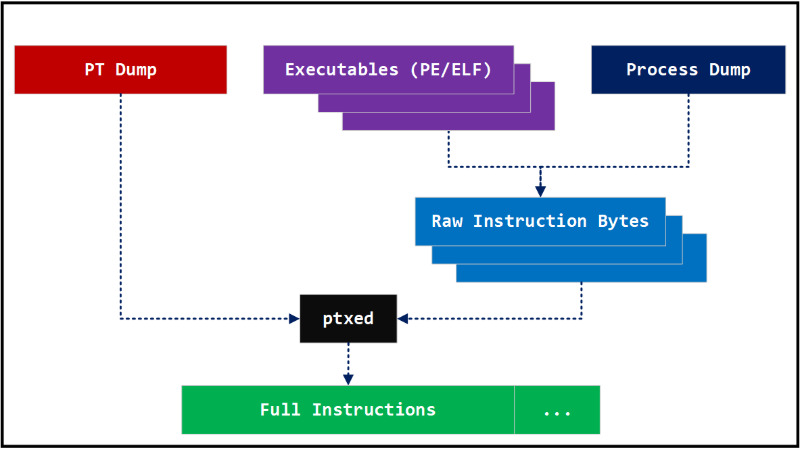
要分析记录的数据包,可以使用Intel的libipt,Libipt是可以解码Intel PT数据包的标准库,它提供了ptdump和ptexd基本工具。
- https://github.com/intel/libipt
https://software.intel.com/en-us/articles/intel-sdm
- 000000000000001c psb
- 000000000000002c pad
- 000000000000002d pad
- 000000000000002e pad
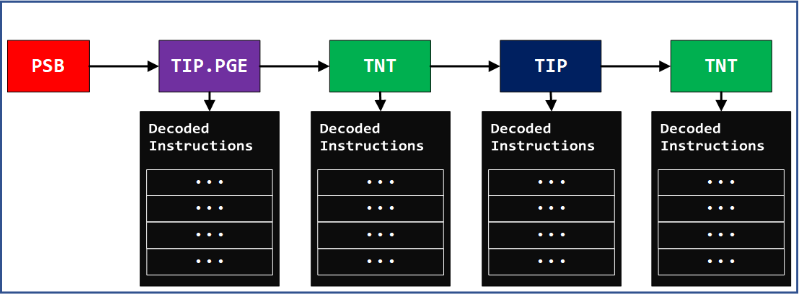
在偏移量3db处,有一个tip.pge数据包。这意味着指令指针位于数据包指示的位置00007ffbb7d63470。
- ...
- 00000000000003db tip.pge 3: 00007ffbb7d63470
- 00000000000003e2 pad
- 00000000000003e3 pad
从过程映像中,我们可以确定tip.pge的地址00007ffbb7d63470指向以下说明。
- seg000:00007FFBB7D63470 mov rcx, [rsp+20h]
- seg000:00007FFBB7D63475 mov edx, [rsp+28h]
- seg000:00007FFBB7D63479 mov r8d, [rsp+2Ch]
- seg000:00007FFBB7D6347E mov rax, gs:60h
- seg000:00007FFBB7D63487 mov r9, [rax+58h]
- seg000:00007FFBB7D6348B mov rax, [r9+r8*8]
- seg000:00007FFBB7D6348F call sub_7FFBB7D63310
提示数据包指示该代码从地址00007ffbb7d63470开始执行,并继续执行直到遇到00007FFBB7D6348F处的调用指令为止。由于调用不是间接调用,因此调用目标是在编译时预先确定的,因此该tip.pge数据包扩展为内部调用指令,来自调用目标地址00007FFBB7D63310的其他指令将被解码。
- seg000:00007FFBB7D63310 sub rsp, 48h
- seg000:00007FFBB7D63314 mov [rsp+48h+var_28], rcx
- seg000:00007FFBB7D63319 mov [rsp+48h+var_20], rdx
- seg000:00007FFBB7D6331E mov [rsp+48h+var_18], r8
- seg000:00007FFBB7D63323 mov [rsp+48h+var_10], r9
- seg000:00007FFBB7D63328 mov rcx, rax
- seg000:00007FFBB7D6332B mov rax, cs:7FFBB7E381E0h
- seg000:00007FFBB7D63332 call rax
此时,在地址00007FFBB7D63332处发生了间接调用,下一个提示包将在此调用跳转的位置提供必要的信息。压缩会删除地址的前4个字节以节省空间,从3ee的数据包中,我们可以得出调用目标是00007ffbb7d4fb70。
- ...
- 00000000000003ee tip 2: ????????b7d4fb70
- 00000000000003f3 pad
- ...
解码从00007ffbb7d4fb70继续,直到它在00007FFBB7D4FB8C处有条件跳转指令为止。
- seg000:00007FFBB7D4FB70 mov rdx, cs:7FFBB7E38380h
- seg000:00007FFBB7D4FB77 mov rax, rcx
- seg000:00007FFBB7D4FB7A shr rax, 9
- seg000:00007FFBB7D4FB7E mov rdx, [rdx+rax*8]
- seg000:00007FFBB7D4FB82 mov rax, rcx
- seg000:00007FFBB7D4FB85 shr rax, 3
- seg000:00007FFBB7D4FB89 test cl, 0Fh
- seg000:00007FFBB7D4FB8C jnz short loc_7FFBB7D4FB95
- seg000:00007FFBB7D4FB8E bt rdx, rax
- seg000:00007FFBB7D4FB92 jnb short loc_7FFBB7D4FBA0
- seg000:00007FFBB7D4FB94 retn
此时,tnt数据包将为你提供是否执行条件跳转的信息。以下带有2个“ ..”的tnt.8数据包表示,它没有进行两次无条件跳转。
- 00000000000003fe tnt.8 ..
接下来,它将在00007FFBB7D4FB94处遇到ret指令。
- seg000:00007FFBB7D4FB94 retn
即使可以通过某种模拟进行计算,也无法从image本身可靠地确定返回地址,“ ret”是间接跳转,它从当前SP(堆栈指针)中检索跳转地址,下一个提示包将为你提供此ret指令返回的地址。
- 00000000000003ff tip 2: ????????b7d63334
返回的地址将按照以下方式反汇编,并且代码执行将继续。
- seg000:00007FFBB7D63334 mov rax, rcx
- seg000:00007FFBB7D63337 mov rcx, [rsp+48h+var_28]
- seg000:00007FFBB7D6333C mov rdx, [rsp+48h+var_20]
- seg000:00007FFBB7D63341 mov r8, [rsp+48h+var_18]
- seg000:00007FFBB7D63346 mov r9, [rsp+48h+var_10]
- seg000:00007FFBB7D6334B add rsp, 48h
https://github.com/ohjeongwook/iptanalyzer
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-11882
https://github.com/ionescu007/winipt https://www.virustotal.com/gui/file/abbdd98106284eb83582fa08e3452cf43e22edde9e86ffb8e9386c8e97440624/detection
- C:\Analysis\DebuggingPackage\TargetMachine\WinIPT>ipttool.exe --trace 2736 EQNEDT32.pt
- /-----------------------------------------\
- |=== Windows 10 RS5 1809 IPT Test Tool ===|
- |=== Copyright (c) 2018 Alex Ionescu ===|
- |=== http://github.com/ionescu007 ===|
- |=== http://www.windows-internals.com ===|
- \-----------------------------------------/
- [+] Found active trace with 1476395324 bytes so far
- [+] Trace contains 11 thread headers
- [+] Trace Entry 0 for TID 2520
- Trace Size: 134217728 [Ring Buffer Offset: 4715184]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 1 for TID 1CA8
- Trace Size: 134217728 [Ring Buffer Offset: 95936]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 2 for TID 8AC
- Trace Size: 134217728 [Ring Buffer Offset: 63152]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 3 for TID 1A88
- Trace Size: 134217728 [Ring Buffer Offset: 4560]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 4 for TID 1964
- Trace Size: 134217728 [Ring Buffer Offset: 45184]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 5 for TID 22D0
- Trace Size: 134217728 [Ring Buffer Offset: 6768]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 6 for TID 73C
- Trace Size: 134217728 [Ring Buffer Offset: 32480]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 7 for TID 1684
- Trace Size: 134217728 [Ring Buffer Offset: 285264]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 8 for TID 3C4
- Trace Size: 134217728 [Ring Buffer Offset: 99056]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 9 for TID 610
- Trace Size: 134217728 [Ring Buffer Offset: 4812464]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace Entry 10 for TID 1CD8
- Trace Size: 134217728 [Ring Buffer Offset: 7424]
- Timing Mode: MTC Packets [MTC Frequency: 3, ClockTsc Ratio: 83]
- [+] Trace for PID 2736 written to EQNEDT32.pt
https://docs.microsoft.com/en-us/sysinternals/downloads/procdump https://docs.microsoft.com/en-us/sysinternals/downloads/process-explorer
- python %IPTANALYZER%\pyipttool\decode_blocks.py -p PT\EQNEDT32.pt -d ProcessMemory\EQNEDT32.dmp -c block.cache
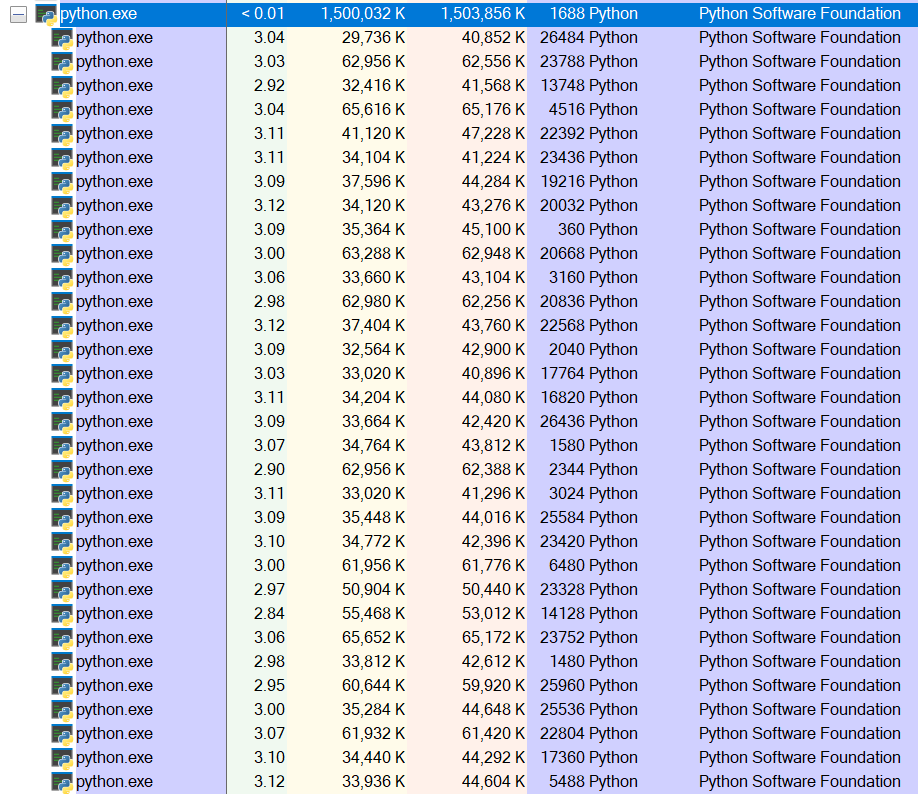
下面显示了并行的Python进程,它们对解码文件进行解码。
- 0:011> lmvm EQNEDT32
- Browse full module list
- start end module name
- 00000000`00400000 00000000`0048e000 EQNEDT32 (deferred)
- ...
dump_blocks.py工具可用于枚举特定地址范围内的任何基本块。
- python %IPTANALYZER%\pyipttool\dump_blocks.py -p PT\EQNEDT32.pt -d ProcessMemory\EQNEDT32.dmp -C 0 -c blocks.cache -s 0x00400000 -e 0x0048e000
该命令将生成与地址范围匹配的基本块的完整日志。从易受攻击的模块执行代码结束时,可能会过渡到shellcode,我们将重点放在日志末尾的基本块模式。注意,“ sync_offset = 2d236c”显示了这些最后的基本块命中的PSB数据包的位置。此sync_offset值可用于检索该点附近的指令。
- ...
- > 00000000004117d3 () (sync_offset=2d236c, offset=2d26f4)
- EQNEDT32!EqnFrameWinProc+0x2cf3:
- 00000000`004117d3 0fbf45c8 movsx eax,word ptr [rbp-38h]
- > 000000000041181e () (sync_offset=2d236c, offset=2d26f4)
- EQNEDT32!EqnFrameWinProc+0x2d3e:
- 00000000`0041181e 0fbf45fc movsx eax,word ptr [rbp-4]
- > 0000000000411869 () (sync_offset=2d236c, offset=2d26f4)
- EQNEDT32!EqnFrameWinProc+0x2d89:
- 00000000`00411869 33c0 xor eax,eax
- > 000000000042fad6 () (sync_offset=2d236c, offset=2d26fc)
- EQNEDT32!MFEnumFunc+0x12d9:
- 00000000`0042fad6 c3 ret
- python %IPTANALYZER%\pyipttool\dump_instructions.py -p ..\PT\EQNEDT32.pt -d ..\ProcessMemory\EQNEDT32.dmp -S 0x2d236c -E 0x2d307c
- ...
- Instruction: EQNEDT32!EqnFrameWinProc+0x2d8b:
- 00000000`0041186b e900000000 jmp EQNEDT32!EqnFrameWinProc+0x2d90 (00000000`00411870)
- Instruction: EQNEDT32!EqnFrameWinProc+0x2d90:
- 00000000`00411870 5f pop rdi
- Instruction: EQNEDT32!EqnFrameWinProc+0x2d91:
- 00000000`00411871 5e pop rsi
- Instruction: EQNEDT32!EqnFrameWinProc+0x2d92:
- 00000000`00411872 5b pop rbx
- Instruction: EQNEDT32!EqnFrameWinProc+0x2d93:
- 00000000`00411873 c9 leave
- Instruction: EQNEDT32!EqnFrameWinProc+0x2d94:
- 00000000`00411874 c3 ret
- Instruction: EQNEDT32!MFEnumFunc+0x12d9:
- 00000000`0042fad6 c3 ret
- Instruction: 00000000`0019ee9c bac342baff mov edx,0FFBA42C3h
- Instruction: 00000000`0019eea1 f7d2 not edx
- Instruction: 00000000`0019eea3 8b0a mov ecx,dword ptr [rdx]
- Instruction: 00000000`0019eea5 8b29 mov ebp,dword ptr [rcx]
- Instruction: 00000000`0019eea7 bb3a7057f4 mov ebx,0F457703Ah
- Instruction: 00000000`0019eeac 81eb8a0811f4 sub ebx,0F411088Ah
- Instruction: 00000000`0019eeb2 8b1b mov ebx,dword ptr [rbx]
- Instruction: 00000000`0019eeb4 55 push rbp
- Instruction: 00000000`0019eeb5 ffd3 call rbx
- ...
从上面的指令清单中,你可以注意到00411874和0042fad6有两个“ ret”指令。
- Instruction: EQNEDT32!EqnFrameWinProc+0x2d94:
- 00000000`00411874 c3 ret
- Instruction: EQNEDT32!MFEnumFunc+0x12d9:
- 00000000`0042fad6 c3 ret
在这两个“ ret”指令之后,代码将转移到非映像地址空间中。
- Instruction: 00000000`0019ee9c bac342baff mov edx,0FFBA42C3h
- Instruction: 00000000`0019eea1 f7d2 not edx
- Instruction: 00000000`0019eea3 8b0a mov ecx,dword ptr [rdx]
- Instruction: 00000000`0019eea5 8b29 mov ebp,dword ptr [rcx]
- Instruction: 00000000`0019eeb7 0567946d03 add eax,36D9467h
- Instruction: 00000000`0019eebc 2d7e936d03 sub eax,36D937Eh
- Instruction: 00000000`0019eec1 ffe0 jmp rax
这些是dump_instructions.py脚本转储的下一阶段shellcode。
- Instruction: 00000000`00618111 9c pushfq
- Instruction: 00000000`00618112 56 push rsi
- Instruction: 00000000`00618113 57 push rdi
- Instruction: 00000000`00618114 eb07 jmp 00000000`0061811d
- Instruction: 00000000`0061811d 9c pushfq
- Instruction: 00000000`0061811e 57 push rdi
- Instruction: 00000000`0061811f 57 push rdi
- Instruction: 00000000`00618120 81ef40460000 sub edi,4640h
- Instruction: 00000000`00618126 81ef574b0000 sub edi,4B57h
- Instruction: 00000000`0061812c 8dbfbc610000 lea edi,[rdi+61BCh]
- Instruction: 00000000`00618132 81c73b080000 add edi,83Bh
- Instruction: 00000000`00618138 5f pop rdi
- Instruction: 00000000`00618139 5f pop rdi
本文翻译自:https://darungrim.com/research/2020-05-07-UsingIntelPTForVulnerabilityTriagingWithIPTAnalyzer.html如若转载,请注明原文地址。