https://supportannouncement.us.dlink.com/announcement/publication.aspx?name=SAP10157
- request admin
服务器响应与三个值的请求:Challenge,Cookie和PublicKey
- OK rEmNZG3LUDFUSMJHU55P uidpiK0+ vq1w3gFhoIAlc38rEVLO 0
客户端必须首先将PublicKey和用户密码结合在一起以创建一个PrivateKey。请注意这一点,因为它将在以后变得很重要。然后,客户端将使用新生成的PrivateKey和Challenge来生成新值。客户端将此值放在消息的LoginPassword字段中,login作为对服务器发出的质询的响应:
- login admin ........
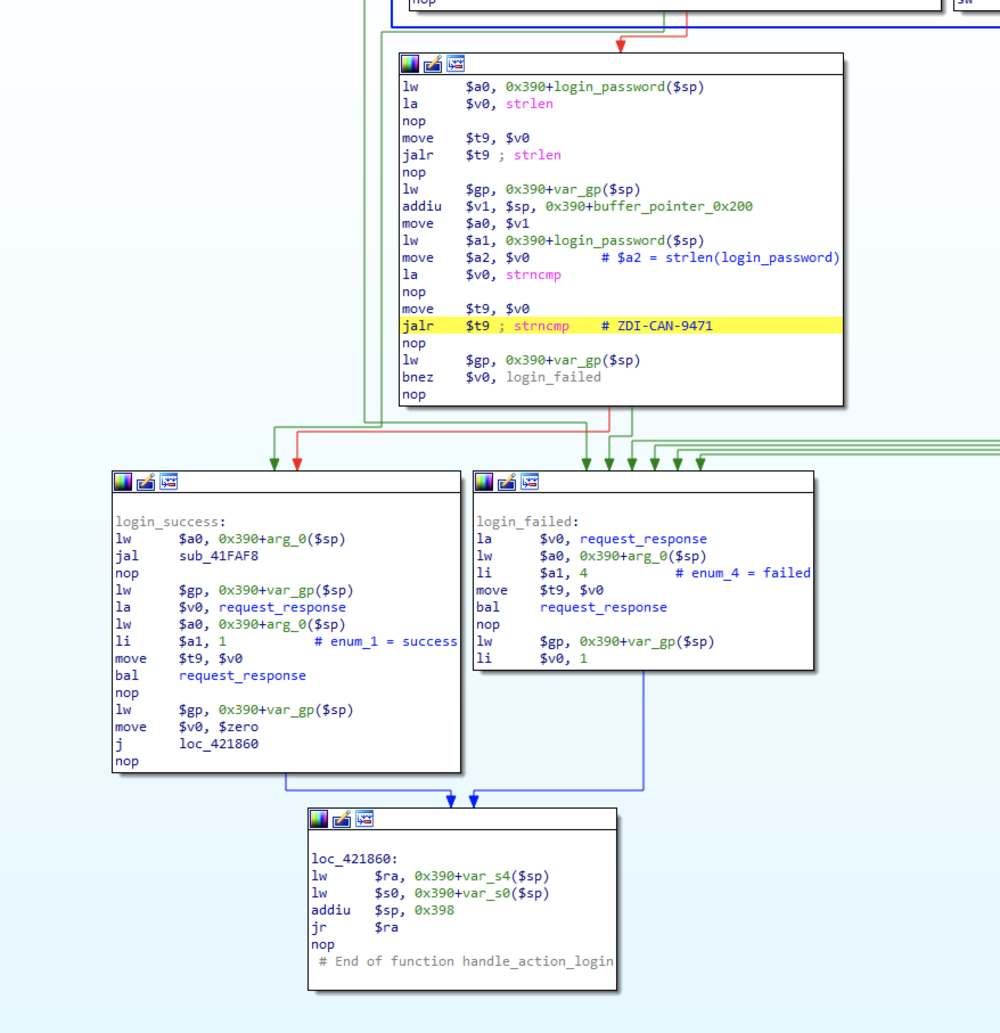
- strncmp(db_password,attacker_provided_password,strlen(attacker_provided_password));
- request Admin Username
以下是生成研究人员提供的身份验证质询值的函数的Ghidra的反编译器输出:
- undefined4 Request(char **param_1,undefined4 param_2,undefined4 param_3,undefined4 param_4) // offset 0x004206c0
- {
- int iVar1;
- char *Username;
- char *Captcha;
- char *PrivateLogin;
- size_t size;
- undefined4 uVar2;
- undefined *Uid;
- char *__nptr;
- int local_1a8;
- char Challenge [64];
- undefined Uuid [64];
- char Publickey [64];
- char Password [64];
- char PrivateKey [132];
- memset(Challenge,0,0x40);
- memset(Uuid,0,0x40);
- memset(Publickey,0,0x40);
- memset(Password,0,0x40);
- uVar2 = 0x80;
- memset(PrivateKey,0,0x80);
- iVar1 = FUN_00421a44(param_1);
- if (iVar1 == 0) {
- webGetVarString(param_1,"/Login/Action",uVar2,param_4);
- Username = (char *)webGetVarString(param_1,"/Login/Username",uVar2,param_4);
- webGetVarString(param_1,"/Login/LoginPassword",uVar2,param_4);
- Captcha = (char *)webGetVarString(param_1,"/Login/Captcha",uVar2,param_4);
- PrivateLogin = (char *)webGetVarString(param_1,"/Login/PrivateLogin",uVar2,param_4); // Get PrivateLogin element
- __nptr = (char *)nvram_safe_get("CAPTCHA");
- iVar1 = atoi(__nptr);
- if ((iVar1 != 0) || (*Captcha != '')) {
- local_1a8 = 0;
- while ((local_1a8 < gCntUid &&
- (iVar1 = strcmp(*(char **)(pgUidCaptMap + local_1a8 * 8),param_1[0x36]), iVar1 != 0)))
- {
- local_1a8 = local_1a8 + 1;
- }
- size = strlen(Captcha);
- ToUpper(Captcha,size);
- __nptr = *(char **)(pgUidCaptMap + local_1a8 * 8 + 4);
- size = strlen(*(char **)(pgUidCaptMap + local_1a8 * 8 + 4));
- ToUpper(__nptr,size);
- iVar1 = strcmp(*(char **)(pgUidCaptMap + local_1a8 * 8 + 4),Captcha);
- if (iVar1 != 0) {
- FUN_0042115c(local_1a8);
- Login_Response(param_1,4);
- return 0;
- }
- FUN_0042115c(local_1a8);
- }
- Randombyte(Challenge,0x14);
- Randombyte(Uuid,10);
- Randombyte(Publickey,0x14);
- // If PrivateLogin != NULL && PrivateLogin == "Username" Then Password = Username
- if ((PrivateLogin == (char *)0x0) || (iVar1 = strncmp(PrivateLogin,"Username",8), iVar1 != 0)) {
- GetPassword(Password,0x40);
- }
- else {
- strncpy(Password,Username,0x40);
- }
- // GenPrivateKey(Challenge, Password = username , PublicKey, PrivateKey, 0x800;
- GenPrivateKey(Challenge,Password,Publickey,PrivateKey,0x80);
- __nptr = Challenge;
- Uid = Uuid;
- uVar2 = SaveCookie(param_1,PrivateKey,__nptr,Uid,Publickey);
- AddCookie(param_1,Uuid,__nptr,Uid);
- Login_Response(param_1,0);
- }
- else {
- Login_Response(param_1,5);
- uVar2 = 1;
- }
- return uVar2;
- }
本文翻译自:https://www.thezdi.com/blog/2020/9/30/the-anatomy-of-a-bug-door-dissecting-two-d-link-router-authentication-bypasses如若转载,请注明原文地址。