0x01 前言
昨日,【CVE 2015-0235: GNU glibc gethostbyname 缓冲区溢出漏洞 】全面爆发,该漏洞的产生是Qualys公司在进行内部代码审核时,发现了一个在GNU C库(glibc)中存在的__nss_hostname_digits_dots函数导致的缓冲区溢出漏洞。这个bug可以通过gethostbyname *()函数来触发,本地和远程均可行。该漏洞(幽灵漏洞)造成了远程代码执行,攻击者可以利用此漏洞远程获取系统进程当前的权限。
鉴于网上诸多glibc的原理普及,本文章就不多啰嗦了,直接实践如何检测服务器是否存在该漏洞,以及修复漏洞的方法。
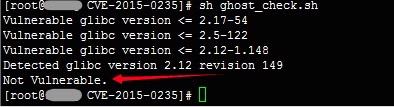
0x02 检测是否存在幽灵漏洞(GHOST)
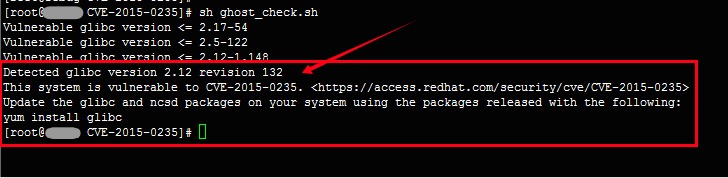
检测方法1【RedHat官方检测方法】:
ghost_check.sh源码:
- #!/bin/bash
- vercomp () {
- if [[ $1 == $2 ]]
- then
- return 0
- fi
- local IFS=.
- local i ver1=($1) ver2=($2)
- # fill empty fields in ver1 with zeros
- for ((i=${#ver1[@]}; i<${#ver2[@]}; i++))
- do
- ver1[i]=0
- done
- for ((i=0; i<${#ver1[@]}; i++))
- do
- if [[ -z ${ver2[i]} ]]
- then
- # fill empty fields in ver2 with zeros
- ver2[i]=0
- fi
- if ((10#${ver1[i]} > 10#${ver2[i]}))
- then
- return 1
- fi
- if ((10#${ver1[i]} < 10#${ver2[i]}))
- then
- return 2
- fi
- done
- return 0
- }
- glibc_vulnerable_version=2.17
- glibc_vulnerable_revision=54
- glibc_vulnerable_version2=2.5
- glibc_vulnerable_revision2=122
- glibc_vulnerable_version3=2.12
- glibc_vulnerable_revision3=148
- echo "Vulnerable glibc version <=" $glibc_vulnerable_version"-"$glibc_vulnerable_revision
- echo "Vulnerable glibc version <=" $glibc_vulnerable_version2"-"$glibc_vulnerable_revision2
- echo "Vulnerable glibc version <=" $glibc_vulnerable_version3"-1."$glibc_vulnerable_revision3
- glibc_version=$(rpm -q glibc | awk -F"[-.]" '{print $2"."$3}' | sort -u)
- if [[ $glibc_version == $glibc_vulnerable_version3 ]]
- then
- glibc_revision=$(rpm -q glibc | awk -F"[-.]" '{print $5}' | sort -u)
- else
- glibc_revision=$(rpm -q glibc | awk -F"[-.]" '{print $4}' | sort -u)
- fi
- echo "Detected glibc version" $glibc_version" revision "$glibc_revision
- vulnerable_text=$"This system is vulnerable to CVE-2015-0235. <https://access.redhat.com/security/cve/CVE-2015-0235>
- Update the glibc and ncsd packages on your system using the packages released with the following:
- yum install glibc"
- if [[ $glibc_version == $glibc_vulnerable_version ]]
- then
- vercomp $glibc_vulnerable_revision $glibc_revision
- elif [[ $glibc_version == $glibc_vulnerable_version2 ]]
- then
- vercomp $glibc_vulnerable_revision2 $glibc_revision
- elif [[ $glibc_version == $glibc_vulnerable_version3 ]]
- then
- vercomp $glibc_vulnerable_revision3 $glibc_revision
- else
- vercomp $glibc_vulnerable_version $glibc_version
- fi
- case $? in
- 0) echo "$vulnerable_text";;
- 1) echo "$vulnerable_text";;
- 2) echo "Not Vulnerable.";;
- esac
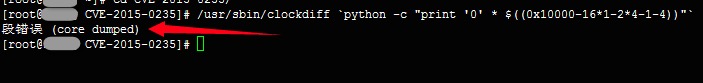
检测方法2【简单的检测方法】:
检测方法2源码:
- /usr/sbin/clockdiff `python -c "print '0' * $((0x10000-16*1-2*4-1-4))"`
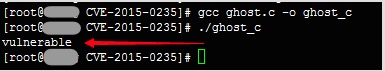
检测方法3【二进制检测方法】:
ghost.c源码:
- #include <netdb.h>
- #include <stdio.h>
- #include <stdlib.h>
- #include <string.h>
- #include <errno.h>
- #define CANARY "in_the_coal_mine"
- struct {
- char buffer[1024];
- char canary[sizeof(CANARY)];
- } temp = { "buffer", CANARY };
- int main(void) {
- struct hostent resbuf;
- struct hostent *result;
- int herrno;
- int retval;
- /*** strlen (name) = size_needed - sizeof (*host_addr) - sizeof (*h_addr_ptrs) - 1; ***/
- size_t len = sizeof(temp.buffer) - 16*sizeof(unsigned char) - 2*sizeof(char *) - 1;
- char name[sizeof(temp.buffer)];
- memset(name, '0', len);
- name[len] = '\0';
- retval = gethostbyname_r(name, &resbuf, temp.buffer, sizeof(temp.buffer), &result, &herrno);
- if (strcmp(temp.canary, CANARY) != 0) {
- puts("vulnerable");
- exit(EXIT_SUCCESS);
- }
- if (retval == ERANGE) {
- puts("not vulnerable");
- exit(EXIT_SUCCESS);
- }
- puts("should not happen");
- exit(EXIT_FAILURE);
- }
#p#
0x03 在线修复方案
CentOS, Red Hat, Fedora等系列衍生版本(RHN建议):
- yum update glibc
Debian, Ubuntu等系列衍生版本:
- apt-get clean && apt-get update && apt-get upgrade
#p#
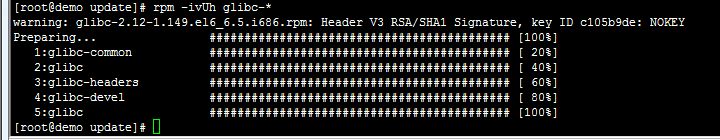
0x04 离线修复方案
Centos6.5离线补丁
先检查本地glibc包安装了哪些相关包
- rpm -qa|grep glibc
然后,到阿里源下载对应版本
- cat > update.txt << EOF
- http://mirrors.aliyun.com/centos/6.6/updates/x86_64/Packages/glibc-2.12-1.149.el6_6.5.i686.rpm
- http://mirrors.aliyun.com/centos/6.6/updates/x86_64/Packages/glibc-2.12-1.149.el6_6.5.x86_64.rpm
- http://mirrors.aliyun.com/centos/6.6/updates/x86_64/Packages/glibc-common-2.12-1.149.el6_6.5.x86_64.rpm
- http://mirrors.aliyun.com/centos/6.6/updates/x86_64/Packages/glibc-devel-2.12-1.149.el6_6.5.x86_64.rpm
- http://mirrors.aliyun.com/centos/6.6/updates/x86_64/Packages/glibc-headers-2.12-1.149.el6_6.5.x86_64.rpm
- EOF
进行后台断点下载补丁包
- wget -b -i update.txt -c
使用yum本地安装
- yum localinstall glibc-*
或是rpm安装
- rpm -ivUh glibc-*
Red Had系列衍生版本
使用方法参考上文【Centos6.5离线补丁】的修补方法
http://mirrors.aliyun.com/centos/7/updates/x86_64/Packages/glibc-2.17-55.el7_0.5.i686.rpm
http://mirrors.aliyun.com/centos/7/updates/x86_64/Packages/glibc-2.17-55.el7_0.5.x86_64.rpm
0x05 修复完成检测
ghost_check.sh脚本检测
ghost.c脚本检测
注意:打好补丁后必须立即重启操作系统,否则会造成应用业务无法使用。
0x06 参考来源
redhat官方
https://access.redhat.com/articles/1332213
redhat官方补丁介绍:
https://rhn.redhat.com/errata/RHSA-2015-0090.html
https://rhn.redhat.com/errata/RHSA-2015-0092.html
ubuntu官方补丁介绍:
http://www.ubuntu.com/usn/usn-2485-1/