最近看了infosec 出品的《Protecting WordPress Installations in an IaaS Environment》,决定给裸奔的wordpress做做安全加固。
wordpress是国人搭建个人博客的首选,其地位等同于论坛搭建首选discuz(话说,discuz才报出全局变量绕过导致的命令执行大洞,唉,开源的APP都是不产蜜而产getshell的蜂巢)
wordpress以丰富的插件(插件漏洞)闻名,因此攻击者一般会对wordpress来个指纹识别(除去找暴力破解/社工后台登陆口的快捷方法)。
一、wpscan – Wordpress指纹识别及漏洞检查工具
该网站被丧心病狂的GFW封掉了,翻墙吧psiphon搔年,或者使用渗透套装kali(重点不是wpscan,了解攻击才能给出相应防御措施)
a.安装
以ubuntu安装为例
apt-get install libcurl4-gnutls-dev libxml2 libxml2-dev libxslt1-dev ruby-dev build-essential git clone https://github.com/wpscanteam/wpscan.git cd wpscan/ gem install bundler && bundle install --without test
b.基本使用
枚举站点信息:用户名、插件、样式等信息
ruby wpscan.rb --url www.tanjiti.com --enumerate
以下是探测结果样本
[+] URL: http://www.tanjiti.com
[+] Started: Tue Oct 28 15:46:30 2014[!] The WordPress 'http://www.tanjiti.com/readme.html' file exists
[+] XML-RPC Interface available under: http://www.tanjiti.com/xmlrpc.php
[!] Upload directory has directory listing enabled: http://www.tanjiti.com/wp-content/uploads/[+] WordPress version 4.0 identified from meta generator
[+] WordPress theme in use: twentyfourteen - v1.2
[+] Name: twentyfourteen - v1.2
| Location: http://www.tanjiti.com/wp-content/themes/twentyfourteen/
| Style URL: http://www.tanjiti.com/wp-content/themes/twentyfourteen/style.css
| Referenced style.css: http://www.tanjiti.com/wp-content/themes/twentyfourteen/style.css
| Theme Name: Twenty Fourteen
| Theme URI: http://wordpress.org/themes/twentyfourteen
| Description: In 2014, our default theme lets you create a responsive magazine website with a sleek, modern des...
| Author: the WordPress team
| Author URI: http://wordpress.org/[+] Enumerating installed plugins (only vulnerable ones) ...
Time: 00:00:37 <==============================================> (880 / 880) 100.00% Time: 00:00:37
[+] No plugins found
[+] Enumerating installed themes (only vulnerable ones) ...
Time: 00:00:16 <==============================================> (308 / 308) 100.00% Time: 00:00:16
[+] No themes found
[+] Enumerating timthumb files ...
Time: 00:01:48 <============================================> (2539 / 2539) 100.00% Time: 00:01:48
[+] No timthumb files found
[+] Enumerating usernames ...
[+] Identified the following 1 user/s:
+----+---------+---------+
| Id | Login | Name |
+----+---------+---------+
| 1 | tanjiti | tanjiti |
+----+---------+---------+[+] Finished: Tue Oct 28 15:49:34 2014
察看详细的探测信息
ruby wpscan.rb --url www.tanjiti.com --debug-output --random-agent >debug.log
(注意:wpscan 默认User-Agent为WPScan v2.5.1 (http://wpscan.org),扫描器使用常识之一使用正常变化的ua,避免触发WAF之类的防御部署)
基本察看LOG,我们就可以知道wpscan是如何收集信息
例如检查响应头X-Pingback: http://www.tanjiti.com/xmlrpc.php 头 (xmlrpc漏洞)
检查xmlrpc.php (xmlrpc漏洞)
检查robots.txt文件 (敏感信息泄露)
检查readme.html文件(敏感信息泄露)
检查/wp-content/debug.log(敏感信息泄露)
检查配置文件(能够明文读取配置文件基本就是挂掉了),wp-config.php.swo,%23wp-config.php%23,wp-config.orig,wp-config.php_bak,wp-config.original,wp-config.php.orig,wp-config.php.old,.wp-config.php.swp,wp-config.php.save,wp-config.bak,wp-config.txt,wp-config.php~ ,wp-config.save ,wp-config.old,wp-config.php.swp (敏感信息泄露)
识别指纹后,一般会去漏洞信息库中查找可以利用的漏洞,例如MSF
#p#
二、MSF-wordpress漏洞利用(已方使用就是漏洞扫描)
msf > search wordpress
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/http/wp_custom_contact_forms 2014-08-07 normal WordPress custom-contact-forms Plugin SQL Upload
auxiliary/dos/http/wordpress_xmlrpc_dos 2014-08-06 normal WordPress XMLRPC DoS
以前段时间有名的XMLRPC DoS为例(漏洞说明见 《[科普]什么是 billion laughs-WordPress与Drupal的DoS攻击有感》)
msf > use auxiliary/dos/http/wordpress_xmlrpc_dos
msf auxiliary(wordpress_xmlrpc_dos) > show options
Module options (auxiliary/dos/http/wordpress_xmlrpc_dos):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no Use a proxy chain
RHOST yes The target address
RLIMIT 1000 yes Number of requests to send
RPORT 80 yes The target port
TARGETURI / yes The base path to the wordpress application
VHOST no HTTP server virtual host
msf auxiliary(wordpress_xmlrpc_dos) > set RHOST www.tanjiti.com
RHOST => xxx
msf auxiliary(wordpress_xmlrpc_dos) > set TARGETURI /
TARGETURI => /wordpress/wordpress/
msf auxiliary(wordpress_xmlrpc_dos) > run
(再次强调,重点不是Metasploit,了解攻击才能给出相应防御措施)#p#
三、wordpress防护——使用ModSecurity进行防护
安装及规则编写的基础知识见《[科普文]ubuntu上安装Apache2+ModSecurity及自定义WAF规则》
vim /usr/share/modsecurity-crs/activated_rules/MY.conf
(1) 添加防御xmlrpc漏洞的规则
SecRule REQUEST_URI "@endsWith /xmlrpc.php" "deny,tag:'WEB_ATTACK/WORDPRESS',msg:'block wordpress xmlrpc.php',id:0000003,phase:2"
service apache2 restart
使用MSF发送攻击包
msf auxiliary(wordpress_xmlrpc_dos) > use auxiliary/scanner/http/wordpress_pingback_access
msf auxiliary(wordpress_pingback_access) > show options
Module options (auxiliary/scanner/http/wordpress_pingback_access):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no Use a proxy chain
RHOSTS yes The target address range or CIDR identifier
RPORT 80 yes The target port
TARGETURI / yes The path to wordpress installation (e.g. /wordpress/)
THREADS 1 yes The number of concurrent threads
VHOST no HTTP server virtual host
msf auxiliary(wordpress_pingback_access) > set RHOSTS www.tanjiti.com
RHOSTS => xxx
msf auxiliary(wordpress_pingback_access) > set TARGETURI /
TARGETURI => /wordpress/wordpress/
msf auxiliary(wordpress_pingback_access) > run
可以看到拦截日志如下
Message: Warning. String match "/xmlrpc.php" at REQUEST_URI. [file "/usr/share/modsecurity-crs/activated_rules/MY.conf"] [line "4"] [id "0000003"] [msg "block wordpress xmlrpc.php"] [tag "WEB_ATTACK/WORDPRESS"]
(2) 添加防御wpscan默认扫描头的规则
SecRule REQUEST_HEADERS:User-Agent "@contains wpscan" "t:lowercase,deny,tag:'WEB_ATTACK/WORDPRESS',msg:'block wpscanner default useragent',id:0000004,phase:1"
再次运行wpscan,可以看到拦截日志如下
essage: Warning. String match "wpscan" at REQUEST_HEADERS:User-Agent. [file "/usr/share/modsecurity-crs/activated_rules/MY.conf"] [line "6"] [id "0000004"] [msg "block wpscanner default useragent"] [tag "WEB_ATTACK/WORDPRESS"]
大伙可以针对性地添加规则,对个人网站而已,添加白规则较之黑规则会事半功倍,这里的示例规则仅仅是抛砖引玉。#p#
四、wordpress防护——屏蔽敏感信息访问
vim /etc/apache2/apache2.conf
<FilesMatch "\.(sw[po]|old|save|bak|orig(?:inal)?|php(?:~|_bak|\x23))$">
Require all denied
</FilesMatch>
service apache2 restart
五、wordpress防护——启用安全头
vim /etc/apache2/conf-available/security.conf
(1) 防止在IE9、chrome和safari中的MIME类型混淆攻击
Header set X-Content-Type-Options: "nosniff"
(2) 防止clickjacking,只允许遵守同源策略的资源(和站点同源)通过frame加载那些受保护的资源。
Header set X-Frame-Options: "sameorigin"
(3) 开启xss防护并通知浏览器阻止而不是过滤用户注入的脚本。
Header set X-XSS-Protection "1;mode=block"
service apache2 restart
六、wordpress防护——登陆口防爆破
一般的方法是设置一个登陆口白名单,但现在越来越多的网站使用CDN服务,明显不再是个好的防护方案
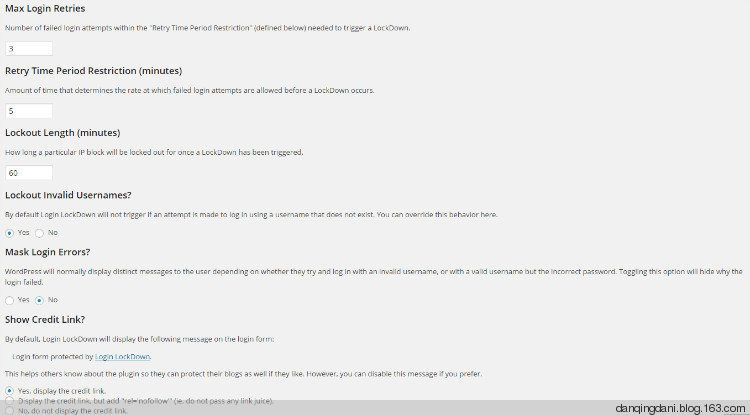
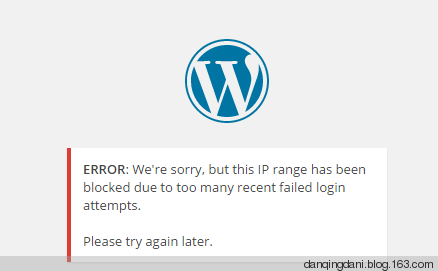
安装Login LockDown 插件,wordpress后台插件管理处搜索即可,设置也超级简单
设置实例:
如果在5分钟失败3次就会封锁IP60分钟